Open ports can be a problem. They might let bad actors into networks. Network bosses use port scanning tools to find and fix these open spots. Not all open ports are bad, though. Some are safely running needed services.
But if we don’t watch them, open ports can cause trouble. They can let in malware, allow sneaky access, and make Denial of Service (DoS) attacks possible. By using good port scanning tools, network pros can spot and seal these openings. This boosts the network’s protection.
The Risks of Open Ports and Unmonitored Services
Open ports with weak security can put networks at risk. They could let harmful software in, allow hackers access, and make DoS attacks possible. Not every service on a port is dangerous. Yet, unwatched open ports can be weak spots in a network.
Attackers can use these open ports to break into network security. They use tools to find open ports and launch attacks. These methods let them check a network, find its weak points, and sometimes get in without permission.
It’s vital for network administrators to keep an eye on open ports and services. This helps prevent security issues and protects network privacy and performance. By managing open ports well, they can spot risks early and keep their networks safe.
Importance of Monitoring Open Ports
Checking on open ports and services is key for network safety. It lets network leaders:
- Spot open ports that shouldn’t be there: Regular checks help find any ports open without a good reason for the network.
- Handle possible weak points: Knowing which services use open ports helps admins fix any vulnerabilities and apply the right security.
- Block unwanted access: Closing open ports fast keeps strangers from getting into the network without permission.
- Find and deal with malware: Watching ports can uncover odd network activity, giving a chance to tackle malware threats.
- Keep the network running smoothly: Proper port management ensures network resources are used well, avoiding slowdowns from unwanted or needless services.
By keeping an eye on open ports and services, network admins can stop security issues before they start. They can run their networks more effectively too.
Minimizing Risks with Firewalls and Access Control
Adding firewalls and access controls improves network safety. Firewalls work as filters, stopping bad traffic and keeping open ports safe. They’re very important for reducing the dangers of open ports and unnoticed services.
Access control lists (ACLs) let admins set rules on who can use open ports, based on IP address, protocol, and port number. Setting up ACLs to limit open port access to trusted sources can cut down threats from outside.
Firewalls and access control steps give an extra safety layer. They lower the risks from open ports and services not being watched closely.
Understanding Port Scanning Tools and Their Benefits
Port scanning tools are key in network security. They automate scanning ports, making work easier for network admins. This lets them find and handle open ports swiftly.
These tools show details of network ports clearly. Network admins can see which ports are open, what services they use, and their response times. This info helps in keeping an eye on ports and checking how they’re used, important for better security.
Advanced port scanning tools update network admins in real-time about port statuses. This lets admins quickly find and secure any open ports. It cuts down the risk of unwanted access.
The Benefits of Port Scanning Tools
Port scanning tools bring many advantages for network security:
- Efficient identification of open ports: They automate finding open ports, making the job easier and faster for network admins.
- Enhanced visibility and monitoring: The tools offer detailed insights into port usage. This aids admins in managing security better.
- Proactive vulnerability detection: By quickly spotting and securing open ports, these tools let admins prevent possible threats early.
- Reduced attack surface: Securing unnecessary ports makes the network safer by limiting access points for attackers.
Port scanning tools are vital for strong network security. They give network admins the right tools and knowledge to guard their networks against dangers.
| Port Scanning Tools | Benefits |
|---|---|
| Automated scanning of ports | Efficient identification of open ports |
| Visibility into network ports | Enhanced monitoring and analysis |
| Real-time port scan statuses | Proactive vulnerability detection |
| Reduction of attack surface | Improved network security |
Introduction to ManageEngine OpUtils – An Advanced Port Scanner
ManageEngine OpUtils is an advanced port scanner designed for network admins. It helps them scan, monitor, and manage ports and network resources at an enterprise level. The toolkit enhances network security and improves port usage.
OpUtils has many useful features for better network management. Some of these features include:
- Switch Port Mapping: It offers detailed mapping of switch ports. This helps network admins easily spot connected devices and fix any connection problems.
- Stacked Port Details: Admins can view and manage ports in stacked switches as one unit. This makes management easier.
- Automated Scan Scheduling: Admins can set up automatic port scans at set times. This ensures ongoing monitoring and early detection of security issues.
- Detailed Reports: OpUtils creates detailed reports. These reports offer insights into port use, aiding in network monitoring and decision-making.
- Threshold-Based Alerting: Admins can set usage limits for ports and get alerts when these limits are passed. This helps prevent network congestion or unauthorized access.
- Resource Monitoring Widgets: The tool provides customizable widgets. These give real-time insights into network resources, helping admins spot and fix issues quickly.
This port scanner makes scanning ports simple and automated. It gives network admins full view and control over their network resources. Using ManageEngine OpUtils helps admins manage ports efficiently, lower security risks, and enhance network performance.
Network Admins Gain Enhanced Network Security with OpUtils
“ManageEngine OpUtils empowers network admins to enhance network security and optimize port usage.”
OpUtils is key in boosting network security through thorough port scanning and monitoring. Admins can identify and handle any open ports that could be security threats. With OpUtils, network security is proactive. It stops unauthorized access and addresses vulnerabilities fast.
The interface of OpUtils is easy-to-use. It allows network admins to set up automated port scans. They can also observe port usage and apply strict security measures. With OpUtils, maintaining a secure and resilient network is easier.
OpUtils works well for networks of any size, including large enterprises. It offers a free 30-day trial. This lets organizations see how well it can scan and manage ports. Beyond port scanning, OpUtils also offers other networking tools and IP address management options. These additions improve network administration efficiency.
With ManageEngine OpUtils as their go-to port scanner, network admins can safeguard their networks. They can also boost performance and streamline their management tasks.
| Key Features of ManageEngine OpUtils | Benefits |
|---|---|
| Switch Port Mapping | Facilitates easy identification of connected devices and swift troubleshooting. |
| Stacked Port Details | Simplifies port management in stacked switches, enhancing overall network efficiency. |
| Automated Scan Scheduling | Enables proactive port scanning and timely detection of security vulnerabilities. |
| Detailed Reports | Provides valuable insights into port usage and assists in informed decision-making. |
| Threshold-Based Alerting | Allows for the setting of usage thresholds and immediate notification of potential network congestion or security breaches. |
| Resource Monitoring Widgets | Real-time visibility into network resources, facilitating quick identification and resolution of issues. |
The Importance of Network TAPs in Network Deployments
Network deployments need smooth network traffic flow for top performance. Network TAPs (Terminal Access Points) are key for this. They make sure new tools and sensors get all the network traffic they need. This helps operations and analysis run smoothly.
Network TAPs are more reliable than SPAN ports, which sometimes lose packets. TAPs feed packets to important tools. Such tools include Network Detection and Response (NDR) and Intrusion Detection System (IDS). They also include Security Information and Event Management (SIEM) and Operational Technology (OT) security sensors.
There are different kinds of TAPs, such as passive or active. They offer flexibility in network setups. These devices can manage traffic in several ways. They ensure network tools get the data they need for keeping things safe and for analysis.
Network TAPs also handle various media types and speeds. They fit into many network settings without issues. Whether using copper, fiber, or higher-speed options, TAPs make sure the network traffic keeps moving well.
Network TAPs in deployments bring many advantages:
- Reliable Traffic Distribution: They make sure all necessary traffic reaches new tools and sensors. This prevents data analysis issues due to missed or dropped packets.
- Enhanced Network Visibility: Network TAPs ensure complete traffic delivery. This gives network managers a full view of network activities. It helps spot potential security risks or performance problems.
- Seamless integration: Network TAPs fit smoothly into current network systems. They do this without stopping the network traffic flow. This makes them a beneficial part of any network setup.
- Increased Scalability: Network TAPs handle different media and speeds. This means they offer flexibility. Network managers can easily grow and adjust their network setups.
- Improved Analytical Accuracy: Because they ensure network tools get all necessary traffic, Network TAPs help in more precise data analysis and security checks. This leads to better threat identification and reaction.
Network TAPs are vital for modern network setups, bringing reliability, insight, and growth ability. They distribute network traffic well to crucial tools and sensors. This ensures strong performance and protection. Adding Network TAPs to network plans helps organizations watch over and secure their networks. This keeps them safe from possible threats and weaknesses.
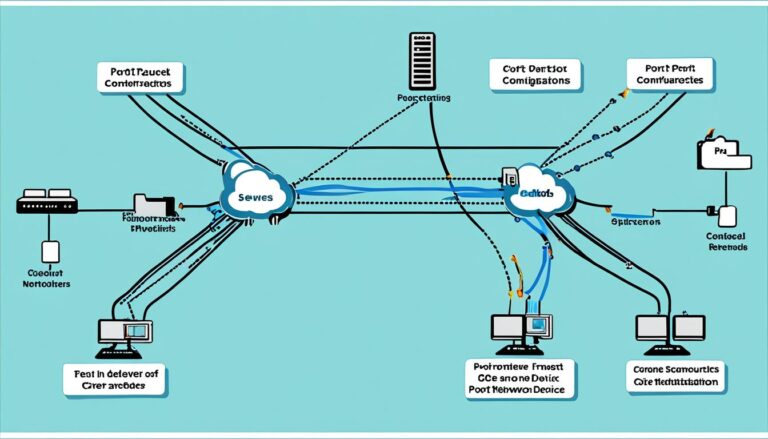
Overcoming Deployment Snags with Network TAPs
When setting up a network, you might face delays due to various snags. These include weak tools, sudden network needs, tricky switches, and issues with SPAN port bidirectionality. To beat these snags, network admins can use network TAPs.
Network TAPs help solve these issues by making sure monitoring tools get all the network data they need. SPAN ports often miss packets if they’re too busy or set up wrong. In contrast, network TAPs ensure traffic flows to tools reliably.
“Network TAPs play a crucial role in overcoming deployment snags by providing essential functionalities that mitigate the impact of these challenges.”
Network TAPs boost tool performance and meet surprise network needs. They offer different ways to connect. This flexibility ensures smooth deployments without risking security or performance.
They are also easy to install and manage. Compared to SPAN ports’ complex setups, TAPs are much simpler. This saves time and resources for network admins.
Below is a table showing how network TAPs outperform SPAN ports:
| Network TAPs | SPAN Ports |
|---|---|
| Ensure all network traffic is received by monitoring tools | Packets can be dropped or missed due to oversubscription |
| Provide alternative connectivity options | Fixed to the physical placement of switches |
| Easy to install and manage | Complex configurations and maintenance |
| Offer flexibility and adaptability | Limitations based on switch capabilities |
This table shows network TAPs’ advantages over SPAN ports. It highlights how they ensure smooth network setup.
Thanks to network TAPs, network admins can move forward confidently. They know they have a solid solution to enhance their network monitoring and security systems.
Hardware Data Diodes for Enhanced OT Network Security
In our digital era, keeping OT networks safe is crucial. These networks run important infrastructures like power and transport systems. Using Hardware Data Diodes improves their security significantly.
These diodes ensure data flows in just one direction at Switch Mirror ports. They stop data from returning to the switch. This action blocks any chance of leaking sensitive info. In cases where we need to see the data, connecting Hardware Data Diodes to SPAN/Mirror ports is smart. It lets us send data to security sensors without risking data flowing both ways.
“Hardware Data Diodes provide an extra layer of security for OT networks by enforcing one-way data flow. This feature helps protect critical infrastructure from potential threats and vulnerabilities.”
Adding Hardware Data Diodes to OT networks boosts their security. This keeps the data safe and sound. At the same time, it cuts down the chance of data leaks or cyber threats happening.
With Hardware Data Diodes, network operators keep their systems safe but still in control. These diodes are key in fighting off cyber threats. They manage risks tied to security weak spots really well.
Advantages of Hardware Data Diodes:
- Enhanced security through one-way data flow.
- Prevention of unauthorized backflow of sensitive information.
- Seamless transmission of mirrored data to monitoring and security sensors.
- Effective blocking of bidirectional traffic flow in OT networks.
- Minimization of the risk of data breaches and cyberattacks.
So, Hardware Data Diodes are key for better OT network security. They ensure data flows only one way and keep out unauthorized access. Putting these diodes into OT networks is a must to protect our vital services in this digital age.
| Advantages of Hardware Data Diodes | |
|---|---|
| Enhanced security through one-way data flow | |
| Prevention of unauthorized backflow of sensitive information | |
| Seamless transmission of mirrored data to monitoring and security sensors | |
| Effective blocking of bidirectional traffic flow in OT networks | |
| Minimization of the risk of data breaches and cyberattacks |
Conclusion
Network TAPs are key for better network security and fixing deployment issues. They make sure network tools get the full traffic flow. This eliminates the chance of losing data packets, improving security.
When deployment problems arise, such as weak tools or unexpected network needs, network TAPs come to the rescue. They ensure all network traffic reaches the right tools. This boosts performance and network clarity. Thus, network admins can manage deployments safely without sacrificing security.
Adding hardware Data Diodes brings more security to OT networks. They ensure data flows just one way. This stops two-way traffic, guarding against threats and risks. It’s a big boost to network security.
Using network TAPs and hardware Data Diodes gives network admins a strong setup. It tackles typical issues and raises network security. These tools make deployments smoother, increase visibility, and shield against security dangers. They lay a sturdy base for a secure network structure.
FAQ
What is a port?
A port is a point where information is sent and received between devices on a network.
What are the risks of open ports and unmonitored services?
Open ports and unmonitored services may allow harmful attacks. These include malware, unauthorized access, and DoS attacks.
What are port scanning tools and what are their benefits?
Port scanning tools help find open ports. They improve security by finding and fixing weak spots in the network.
What is ManageEngine OpUtils and how does it work as an advanced port scanner?
ManageEngine OpUtils is an advanced tool for scanning ports. Network admins can track and control large network ports.
It provides mapping, automated scans, and alerts. This boosts network security.
Why are network TAPs important in network deployments?
Network TAPs help tools view all traffic. They fix SPAN port issues like packet loss. This makes networks more reliable and visible.
How can network TAPs help overcome deployment snags?
Network TAPs solve deployment issues. They guarantee full traffic visibility to tools and offer easy solutions without SPAN complexities.
What are hardware Data Diodes and how do they enhance OT network security?
Hardware Data Diodes strengthen OT security. They allow data to move one way, adding protection against threats and leaks.
Source Links
- https://www.garlandtechnology.com/blog/dont-let-snags-unravel-it-or-ot-network-deployments
- https://blogs.manageengine.com/network/oputils/2021/03/23/unraveling-open-port-threats-and-enhancing-security-with-port-scanning-tools.html
- https://www.linkedin.com/pulse/unraveling-mysteries-sherlock-holmes-tech-ryan-davies-zsdhc